Building a Strong Cybersecurity Posture in 10 Steps
In today’s digital age, businesses of all sizes are vulnerable to cyber attacks. Cybersecurity refers to the practice of protecting devices, networks, and sensitive information from unauthorized access, theft, and damage caused by malicious cyber threats such as viruses, malware, and hackers.
Having a strong cybersecurity posture is critical for businesses to ensure the safety of their data, prevent financial losses, maintain the trust of their clients, and avoid legal consequences. Cyber attacks can cause significant damage to a business’s reputation and bottom line, which is why it’s crucial for organizations to prioritize cybersecurity and take proactive measures to protect themselves.
This article provides a comprehensive guide to help businesses strengthen their cybersecurity posture by outlining the basic steps they can take to protect their networks and data, as well as a cybersecurity checklist with essential measures that should be implemented. Additionally, the article includes best practices for maintaining cybersecurity and engaging with managed IT services providers. By following the steps outlined in this article, businesses can significantly reduce their vulnerability to cyber threats and enhance their overall cybersecurity posture.
Understanding Cybersecurity Threats
Cybersecurity threats are an ever-present danger to businesses of all sizes. It’s essential to understand the different types of threats and their potential impact to take the necessary steps to prevent them.
Malware is one of the most common cybersecurity threats. It refers to malicious software designed to damage, disrupt, or gain unauthorized access to a computer system or network. Phishing is another threat that targets individuals through emails or messages containing malicious links or attachments. Social engineering is yet another type of threat that exploits human behavior to gain access to sensitive information.
The consequences of a cyber attack can be devastating for a business. For example, a malware attack can lead to data loss, downtime, and financial losses. In contrast, a phishing attack can result in identity theft, financial fraud, and reputational damage. Social engineering attacks can be even more harmful, leading to confidential data breaches or intellectual property theft.
Real-world examples of cyber attacks and their consequences are numerous. In 2017, the WannaCry ransomware attack affected over 300,000 computers in 150 countries, causing widespread damage to businesses and organizations worldwide. The 2020 SolarWinds breach was another high-profile attack that targeted several US government agencies and businesses, resulting in the theft of sensitive data.
In summary, understanding the various types of cybersecurity threats and their potential impact is crucial for businesses to develop effective cybersecurity strategies. By doing so, businesses can take proactive measures to prevent cyber attacks, minimize damage, and protect themselves and their clients’ sensitive information.
Basic Steps to Strengthen Cybersecurity Posture
To establish a robust cybersecurity posture, businesses must take some fundamental steps to ensure the security of their networks and data. Below are some basic steps that organizations can take to enhance their cybersecurity posture:
- Conducting a Security Risk Assessment:
A security risk assessment involves identifying and evaluating potential risks and vulnerabilities that a business may face. By conducting a security risk assessment, businesses can develop a plan to mitigate and manage the identified risks.
- Implementing a Strong Password Policy:
A strong password policy is an essential aspect of cybersecurity. It involves creating complex passwords that are difficult to guess and changing them regularly. Passwords should be at least 12 characters long and include a combination of letters, numbers, and special characters.
- Regularly Updating Software and Security Systems:
Regularly updating software and security systems helps to ensure that all systems and applications are patched and up-to-date. This practice can help prevent potential vulnerabilities from being exploited by cyber attackers.
- Enabling Two-Factor Authentication:
Two-factor authentication (2FA) adds an additional layer of security to the login process by requiring a user to provide a second factor, such as a fingerprint or a code sent via SMS, in addition to a password.
- Providing Cybersecurity Awareness Training for Employees:
Cybersecurity awareness training for employees is crucial to prevent social engineering attacks and educate them about potential threats. Employees should be trained to recognize phishing emails, how to respond to suspicious emails, and how to report potential security incidents.
- Implementing a Firewall:
A firewall acts as a barrier between a business’s internal network and the internet, blocking unauthorized access to the network. It can help prevent malware from infiltrating a network and provide an additional layer of security.
- Backing up Data Regularly:
Regularly backing up data is essential to ensure that critical information is not lost in the event of a cyber attack. Businesses should establish a backup strategy that includes backing up data to a secure, off-site location.
- Restricting Access to Sensitive Information:
Limiting access to sensitive information to only authorized personnel can help prevent data breaches. This can be achieved by implementing access control mechanisms such as user permissions, role-based access control, and multi-factor authentication.
- Implementing Anti-Malware and Anti-Virus Software:
Anti-malware and anti-virus software can help detect and prevent malware and viruses from infecting a network. These software solutions should be kept up-to-date to ensure that they are capable of identifying the latest threats.
- Establishing an Incident Response Plan:
An incident response plan outlines the steps that a business should take in the event of a cybersecurity incident. It should include procedures for detecting and responding to an incident, containing the damage, and restoring normal operations.
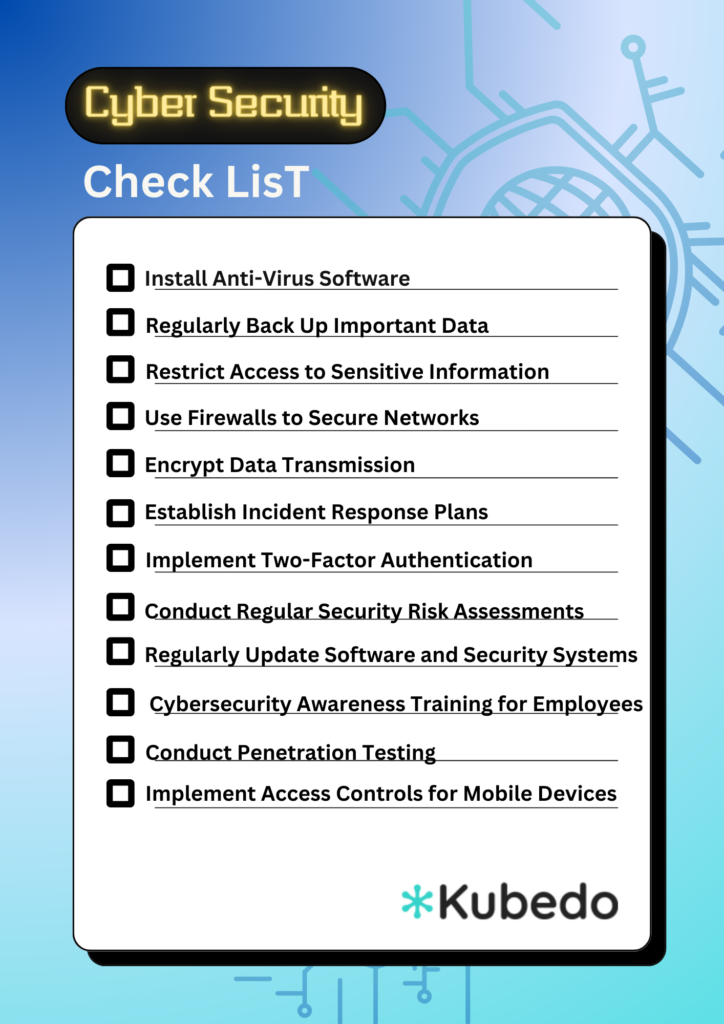
Cybersecurity Checklist
To help businesses protect themselves from cyber threats, we have compiled a comprehensive cybersecurity checklist of essential measures that should be taken to establish a strong cybersecurity posture.
Throughout this article, we have covered a range of important topics related to cybersecurity, including the different types of cybersecurity threats, basic steps to strengthen cybersecurity posture, and a comprehensive cybersecurity checklist. As we wrap up this article, it is important to recap the key points covered and emphasize the importance of taking cybersecurity seriously.
Firstly, businesses need to understand the different types of cybersecurity threats and their potential impact on their operations. Cyber attacks can result in significant financial loss, damage to reputation, and legal liability. By taking a proactive approach to cybersecurity, businesses can significantly reduce their risk of experiencing a cyber attack and the associated consequences.
Secondly, we have highlighted the basic steps that businesses can take to strengthen their cybersecurity posture, such as conducting a security risk assessment, implementing a strong password policy, regularly updating software and security systems, enabling two-factor authentication, and providing cybersecurity awareness training for employees. By following these basic steps, businesses can establish a strong foundation for their cybersecurity posture.
Finally, we have provided a comprehensive cybersecurity checklist that covers essential measures that businesses should take to protect themselves from cyber threats. By implementing these measures, businesses can establish a more comprehensive and effective cybersecurity posture.
In conclusion, cybersecurity is a critical issue that businesses need to take seriously. As the threat landscape continues to evolve and become more sophisticated, it is important for businesses to invest in a strong cybersecurity posture to protect themselves from cyber attacks. We urge all businesses to take action and implement the measures outlined in this article to establish a more secure and resilient cybersecurity posture.